Blacklotus Windows UEFI Malware Source Code Leaked From Darkweb Forum
The Blacklotus Windows UEFI malware has had a portion of its source code posted on GitHub. This could be a big problem for Windows users because now anyone can easily download and run the malware.
BlackLotus is a type of software that targets Windows and can get around the Secure Boot feature, which normally stops untrusted software from running on computers with UEFI firmware and a TPM chip. This feature is meant to prevent harmful programs from loading during startup and to avoid detection by Windows applications.
BlackLotus can also turn off BitLocker Data Protection, Microsoft Defender Antivirus, and Hypervisor Code Integrity (HVCI) protection, which is also called the Memory Integrity feature. HVCI protects against attempts to take advantage of the Windows kernel.
BlackLotus was the first example of a UEFI software that could bypass the Secure Boot feature and disable security measures in the operating system. It did this by exploiting a vulnerability called "Baton Drop" (CVE-2022-21894), but Microsoft fixed it in January 2022.
This led to another security update for CVE-2023-24932, which was another way the Secure Boot feature could be bypassed. This update took away other harmful boot managers.
But here's the problem: Microsoft has disabled the update for CVE-2023-24932 by default. That means Windows users have to go through a long and somewhat complicated process to manually install the fix for their systems.
Microsoft has warned that if you install a security patch incorrectly, your system might not start or recover properly, so many people choose not to install the update. This leaves their devices vulnerable to attacks that can get around the Secure Boot feature.
Because the BlackLotus malware is so worrisome and hard to detect, both Microsoft and the NSA have provided a guide on how to find and remove the malware from Windows.
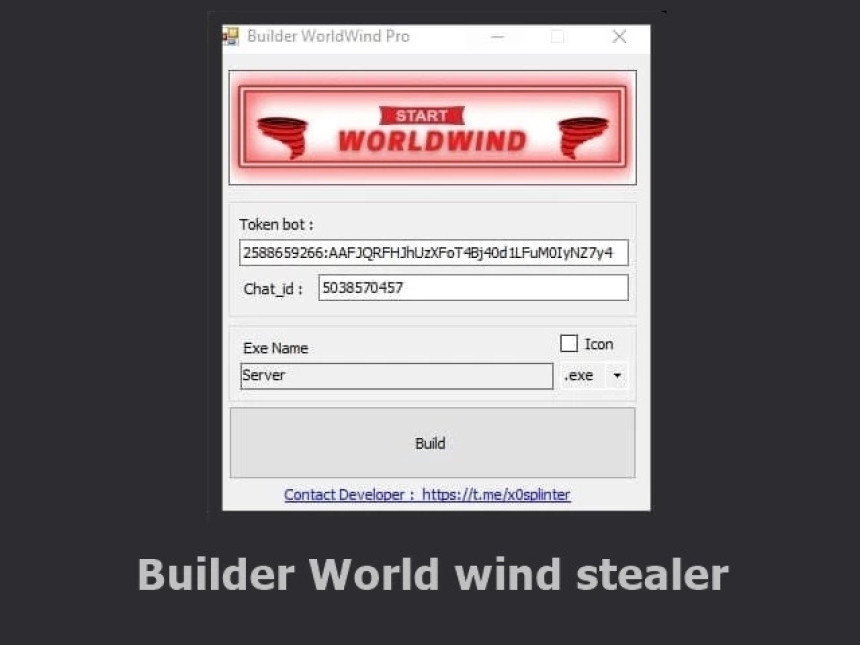
Originally, BlackLotus was being sold on hacker forums for as little as $5,000, which made it accessible to attackers of all skill levels. However, the source code was kept secret, and customers who wanted to customize the software could pay $200 to have it modified.
Now, Binarly, a company that deals with malware, has announced that the source code for the BlackLotus UEFI software has been shared on GitHub by a user called "Yukari".
Yukari claims to have made changes to the source code to remove the Baton Drop vulnerability and instead uses a different rootkit called UEFI bootlicker. This rootkit is based on other rootkits like UEFI APT CosmicStrand, MoonBounce, and ESPECTRE.
"The leaked source code is not complete and mainly includes parts of the rootkit and bootloader code to get around Secure Boot," explained Alex Matrosov, co-founder and CEO of Binarly.
It's important to note that while Microsoft has fixed the Secure Boot bypasses in CVE-2022-21894 and CVE-2023-24932, the security update is optional and the patches are not enabled by default.